I’ve become pretty convinced that self-sovereign keys and trustless protocols are critical if you want to achieve decentralization, user ownership, or credible exit.
Self-sovereign is just a fancy way of saying “it belongs to you”. Self-sovereign keys are keys that live on your device, usually in something like Secure Enclave.
Trustless means “it works all by itself”. You don’t need permission from an authority for the protocol to work.
When I talk about this stuff, I am often met with a reasonable objection: people forget their passwords and lose their keys all the time! They might need an authority to recover their account. So, I want to embrace this point, and respond with three claims:
Trustless protocols are better than trustful ones
Even when you layer key custody on top
But trustless with non-custodial key recovery is best of all
This might seem contradictory, but there are significant differences between a trustful protocol and a trustless one with custody. The most important is that trustless protocols support both trustless and trustful use.
Trustful means “controlled by an authority”
Most of the internet runs on trustful protocols. Any time you “log in” to an app using a username and password, you’re using a trustful protocol. Under the hood, you’re asking an authority, such as Facebook, to authorize you to use a service. They own your account, you just access it. Trustful protocols are trustful because you trust the authority to own your stuff.
It’s reasonable to expect that when you create something, you should own it. But trustful protocols violate this expectation. The authority who manages your account ultimately owns your stuff, because they can revoke your access to it. This is a chokepoint that gives authorities strong leverage for centralization and lock-in.
It’s also reasonable to expect that a private message is private, and there won’t be any eavesdroppers listening in. But trustful protocols violate this expectation as well. Any time you use a trustful protocol to communicate with a friend, there are three people in the chat: you, your friend, and the authority who controls your accounts.
So why did most of the internet get built on top of trustful protocols?
Partly for practical reasons. People need help recovering their accounts, from time to time. People lose passwords. That’s normal. An authority can help with that.
Partly down to chance. In the beginning, the web didn’t have auth, so websites rolled their own, resulting in the fundamentally feudal web we have today.
Either way, the bulk of the internet is built around trustful protocols. Very little of what we do online is actually private, very little actually belongs to us. Centralization and lock-in are common.
This has lead some decentralized projects to try a different approach: trustless authentication.
Trustless means “you’re in control”
When you use a trustless protocol, you don’t need an authority to authorize you. You can authorize yourself. How? By using plain old cryptographic keys at the protocol layer. No login, no password. Just keys.
Crypto wallets are one example of a trustless protocol. Each secure wallet is just a keypair—a public key you share with others, and a private key that gives you access to move funds.

Note that trustless authentication has nothing to do with blockchains per se. This is just ordinary public key cryptography we’re talking about. Using public keys for authentication has been around since PGP. Yet, for whatever reason, it took crypto to push the idea into the mainstream.
One of the lessons from the theory of natural selection is that a degree of isolation can be a great help to a new strategy in gaining a foothold.
(Cosma Shalizi, 1999. "What can emergence tell us about today's Eastern Europe?")
Just use keys! While it may have crawled out of the hot primordial soup of crypto, this little idea has legs. It’s a simple and a good idea, and is being exapted to existing infrastructure in operating systems, web standards proposals, and drafts.
When your protocol is designed around self-sovereign keys, it becomes trustless, and this brings important benefits:
You don’t need to ask an authority to access your stuff. Keys are self-certifying.
You can communicate privately person-to-person, without a man-in-the-middle.
There is no central authority, so there is no auth chokepoint to leverage for lock-in.
Crypto people have a slogan for this: “not your keys not your coins”, and this is true, but it also cuts both ways. We’ve all seen stories of crypto people misplacing their keys and losing millions. So, ownership is important, but it also comes with risks. If you lose your keys, no one can help you. That’s not great.
Luckily we have a way to deal with this IRL. We create a spare key.
Custody means handing your private key to a third party
Why would you do this? For the same reason you might give a friend a spare key to your apartment. If you lose your key, you can always call your friend to let you in.
Funnily enough, custody is how most people use crypto. There are a few ways to do this. You can put a spare key in a hardware wallet, for example. But the most common is to use a service. A service like Coinbase acts as a custodian for your keys. You log in to Coinbase, they keep your spare.
So wait, now we’re all the way back to trusting a third party, right? Well, yes, but…
Trustless with custody is still better than trustful
There are significant strategic differences between the two.
Trustless allows for both trustful and trustless use. You can always implement key custody on top of user-owned keys. If you want key custody, you can have key custody. If you want a cold wallet, you can have a cold wallet. Trustful protocols bake assumptions about authority directly into the infrastructure. Trustless protocols give you the choice.
You can choose your custodian. Does Facebook Connect let you choose a different custodian? No. You’re locked in. Trustless protocols are different. Keys are keys. You get to choose who holds them… or doesn’t. The protocol doesn’t care.
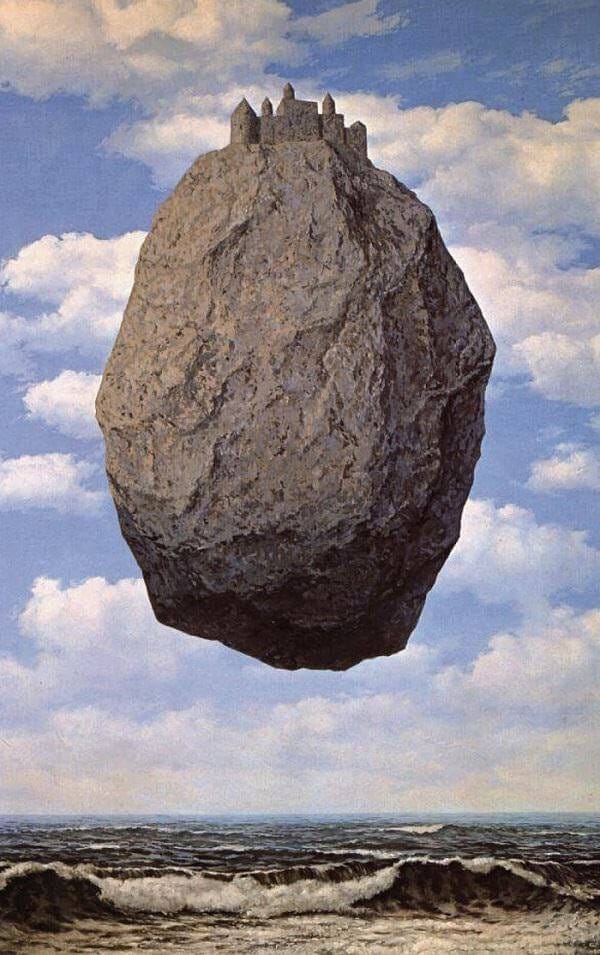
Keys are a lego dot. Products are like lego sets. Protocols are like lego. Imagine if lego changed the shape of the dots. You would have to throw out all your old pieces! Protocol interfaces can’t change without breaking the ecosystem, so, it’s important to find the right “lego dot”.
A protocol interface should be both fundamental and universal. Something that can be used to build many different things. A dot. When you find the right dot, it allows for layering, shearing, and open-ended evolution.
The goal of all theory is to make the basic elements as simple as possible without having to surrender the adequate representation of experience. (Einstein)
Keys are the lego dot of authorization and authentication. They are the basic element of cryptography, the simplest thing that could possibly work. You need keys to sign everything, you need keys to implement end-to-end encryption. Keys are both necessary and sufficient. Just use keys.
Noncustodial key recovery would be best of all
So trustless protocols enable trustless use, through cold wallets, or trustful use, through custody. But they can also enable a third thing: noncustodial key recovery.
Noncustodial key recovery has not been widely productized, because until recently, there were no widely deployed products that just used keys. That’s starting to change. Some wallets offer new forms of recovery that don’t require trusting an authority. These include:
Social key recovery breaks your private key into pieces. You can give these pieces to your friends as a backup. Alone, each piece does nothing, but combine enough of them together and you get your private key. So, if you lose your key, you just hit up your friends, and voilà.
ZK-based key recovery. Further out, we can see schemes to enable noncustodial key recovery through ZK-SNARKS, a clever mathy way to prove that something is true, without revealing any other information. This is new cryptographic magic that I won’t pretend to understand, but there are lots of smart people working on it, and my bet is that they will make a breakthrough.
Here’s the thing—keys are a fundamental universal interface. A lego dot. When you build around a universal interface, you can swap out the old thing for the future better thing when it becomes available. Take off the custodial brick, put on the noncustodial ZK brick. The lego dot stays the same, so you don’t have to throw out all your pieces.
A very little key will open a very heavy door. (Charles Dickens)
Just use keys.



