Cheating Zooko’s Triangle?
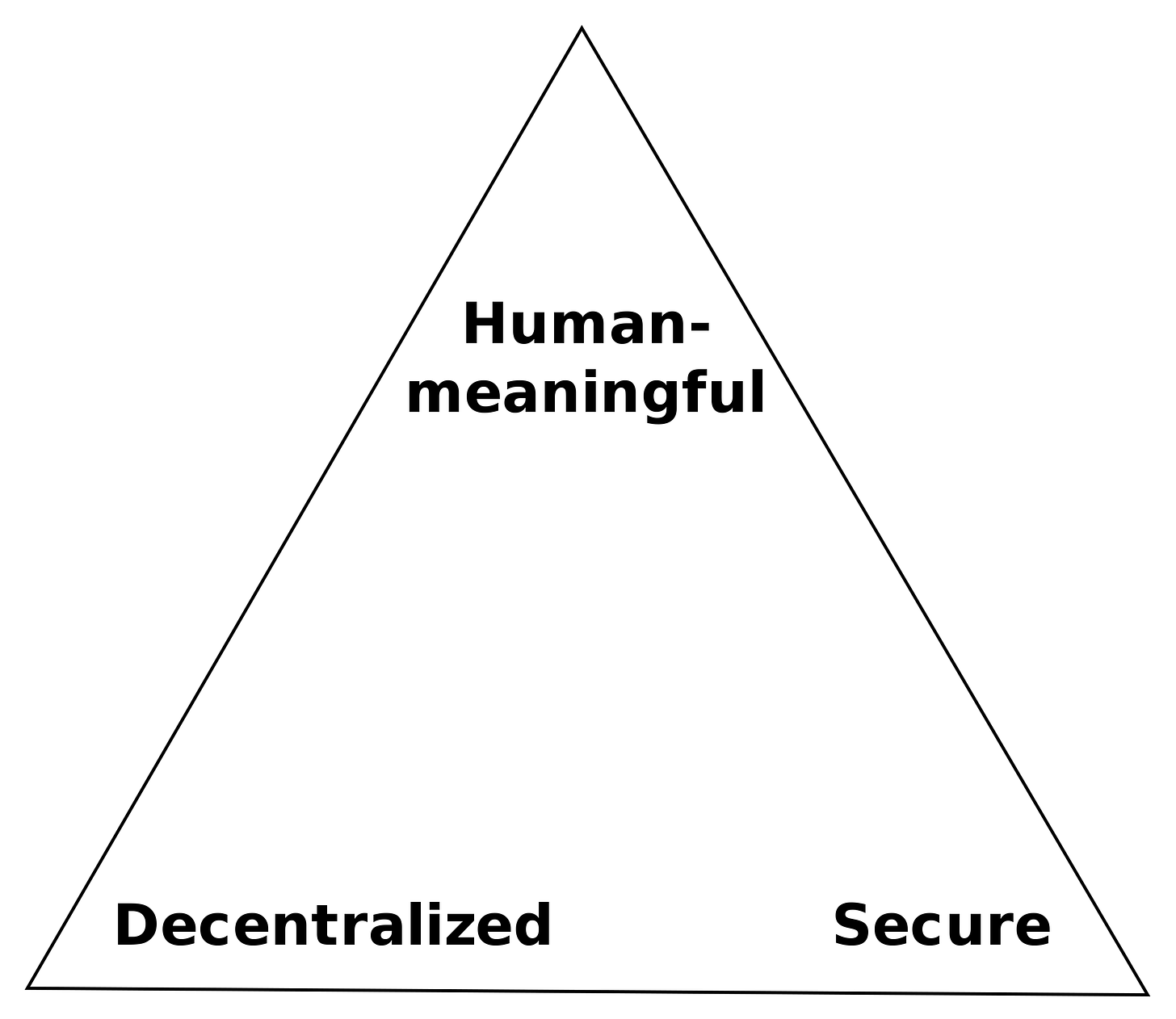
There are three ideal properties you want from a good naming system:
Secure. The name reliably points to what it is supposed to, and not to an imposter.
Decentralized. there is no central authority in the naming system that can fail, or be corrupted.
Human-meaningful. The name makes sense and is memorable. gordonbrander.com, or @gordonbrander, for example.
But there’s a problem! Zooko’s Triangle states that we can’t have all three.
Secure, decentralized, meaningful, pick two.
Zooko’s triangle emerges because there is contention over meaningful names. Names are a scarce resource. I want the username @gordon. All the other Gordons want it too. Vitalik wants @vitalikbuterin. Plenty of spammers and scammers want that username too. Someone has to mediate this conflict.
Faced with this dilemma, systems typically make one of two tradeoffs:
Secure-meaningful addresses use a centralized authority to resolve naming, retaining meaning at the expense of decentralization. Examples: Twitter usernames, and DNS, who’s nameservers are decentralized, but who’s security model is centralized around the authority of ICANN.
Secure-decentralized addresses use hashes or cryptographic keys to prevent naming collisions, retaining decentralization at the expense of meaning. Examples: IPFS content addressing, Urbit IDs, and public-key authentication.
Most user-facing systems choose secure-meaningful centralized addresses.
Squaring Zooko’s Triangle with a Blockchain
But is there another way? Can we get all three? Well, sort of.
Secure Property Titles (Szabo, 1998) shows that you can have secure, decentralized, meaningful addresses… up to the limits of byzantine fault tolerance. The security guarantees break if a large enough portion of the decentralized system cheats.
Byzantine fault tolerance, ay? This sounds kind of like blockchain. And indeed, way back in 2011, Aaron Swartz realized you can square Zooko’s Triangle with a blockchain. The economic incentives around a blockchain make it Byzantine fault tolerant, so you can “mint” names on-chain without a central authority. This is actually not too different from an NFT, and it’s how ENS works.

But what if you wanted to sidestep a blockchain?
Why not both?
Secure-meaningful, or secure-decentralized… why not both? What if we imagine a layered protocol, where secure-meaningful names dereference to secure-decentralized IPFS CIDs?
L1: secure-decentralized CIDs point to an immutable snapshot, and say “these are the bytes”.
L2: secure-meaningful names point to the latest CID for a name, and say “this is what thing (bytes) means for me (origin/key) at this time (of access)”
Choose your Zooko’s Triangle tradeoff a la carte.
This indirection is analogous to the indirection between DNS and IP addresses, but adds another layer (CIDs) in-between, to decouple identifier from locator.
It is generally recognized that the current approach of using IP address both as a locator and as an identifier was a poor design choice.
(Clark, 2018. Designing an Internet)
The indirection doesn’t actually solve Zooko’s Triangle—the centralized name system could still be corrupted—but it does make it easier to do some useful things:
Names become a mechanism for discovering CIDs. CIDs offer a form of credible exit. Because CIDs are secure-decentralized, the network can continue to serve CIDs, and you can continue to refer to snapshots by name, up until the moment the centralized name system failed. Include a parent CID header, and you can trace back the entire history as well. Resilient.
Origins stop mattering so much. Since everything is a CID at the end of the day, and CIDs are secure-decentralized, we don’t have to base security on which server something comes from.
Name pluralism. Many roads lead to the same destination. Since different names can point to the same secure-decentralized CID substrate, we can start to map synonyms. Interesting!
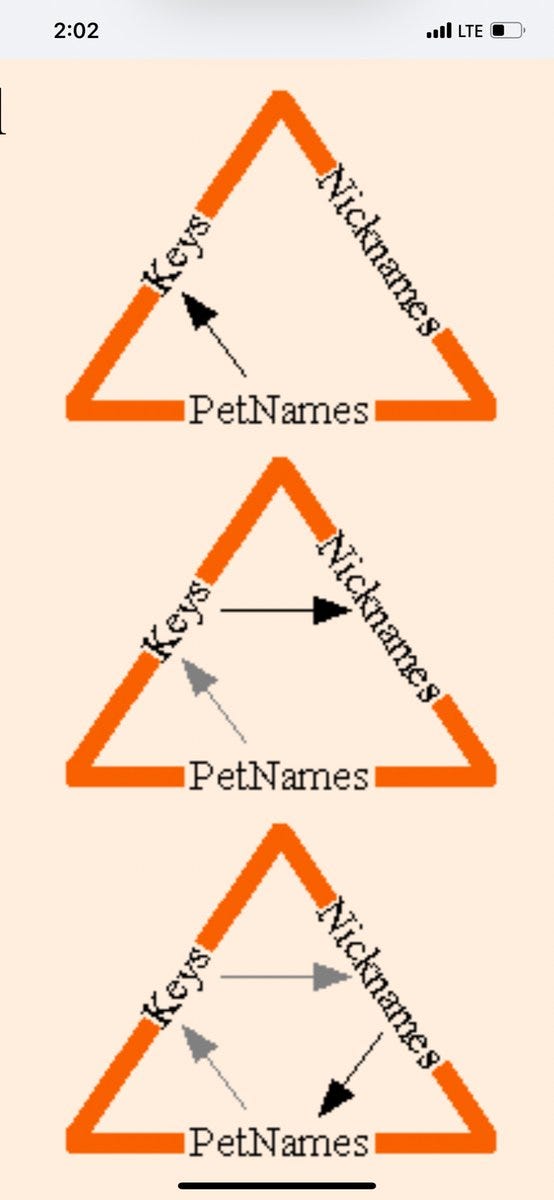
Cheating Zooko’s Triangle with Petnames
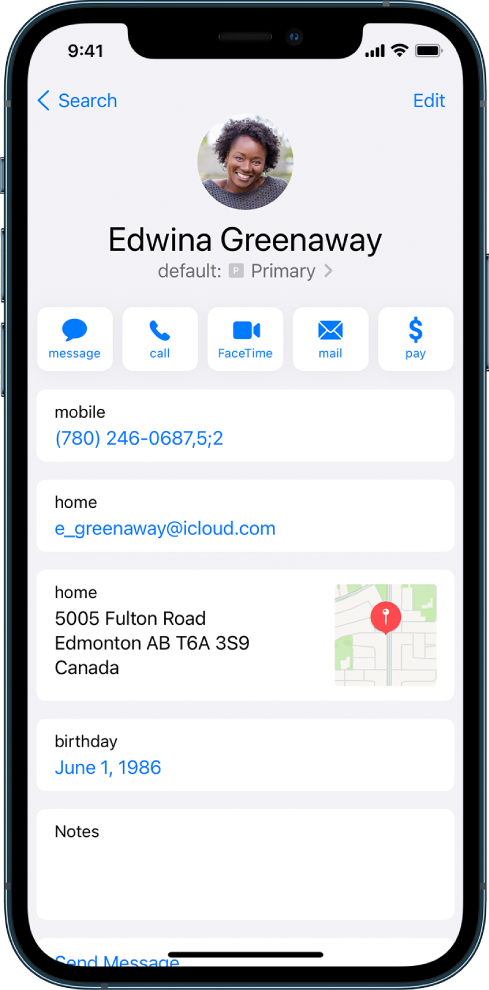
We can go one step further by making names into petnames. A petname system works like the address book on your phone. Instead of a global name system, you keep a personal address book that maps meaningful names to secure-decentralized addresses.
You can also share address books. Peers who trust each other can exchange cryptographic keys, and securely share their petnames, building up webs of trust. Once you’ve exchanged keys, you can securely share updates to your address book as often as you like.
And really, the system we’ve imagined above is most of the way to a petname system. All we have to do is go one step further, and treat the global name system as a way to bootstrap our petname address book. Once bootstrapped, we can continue to securely gossip names within our web of trust, even after the global name system fails.

More links
Introduction to petname systems (Marc Stiegler, 2005)
Rebooting the web of trust (2018)
Backchannel petname system (Ink and Switch, 2021)